Descripción
Acceso seguro en WordPress con este plugin de identificación de dos factores (TFA/2FA). Los usuarios para los que esté habilitado necesitarán un código de un solo uso para acceder. De los autores de UpdraftPlus – el plugin de copia de seguridad/restauración número 1 de WP , con más de dos millones de instalaciones activas.
¿Eres completamente nuevo en TFA? Si es así, consulta nuestras preguntas frecuentes.
Características (consulta las «Capturas de pantalla» para obtener más información):
- Admite los protocolos estándar TOTP + HOTP (por lo que es compatible con Google Authenticator, Authy y muchos otros).
- Muestra códigos QR gráficos para escanear fácilmente en aplicaciones en tu teléfono/tableta
- TFA puede estar disponible por perfil (por ejemplo, disponible para administradores, pero no para suscriptores)
- Cada usuario puede activar o desactivar TFA
- TFA can be required for specified user levels, after a defined time period (e.g. require all admins to have TFA, once their accounts are a week old) (Premium version), including forcing them to immediately set up (by redirecting them to the page to do so)
- Admite la edición de ajustes de portada, a través del shortcode [twofactor_user_settings] (es decir, los usuarios no necesitan acceso al escritorio de WP). (La versión Premium permite el diseño personalizado de cualquier diseño que desees).
- Los propietarios de sitios pueden permitir «dispositivos de confianza» en los que los códigos TFA solo se pidan durante un número determinado de días (en lugar de cada acceso); p.ej. 30 días (versión Premium)
- Encrypt the TFA-generating secret keys using an on-disk encryption key, so that an attacker would need to break into both your WordPress database and your files in order to break TFA codes (as well as breaking a user’s password in order to use them)
- Funciona junto con «Theme My Login» (tanto formularios como widgets)
- Incluye compatibilidad para los formularios de acceso de WooCommerce y Affiliates-WP
- Includes support for Ultimate Membership Pro
- Includes support for CozmosLabs Profile Builder
- Includes support for Ultimate Member login forms (Premium version)
- Incluye compatibilidad para formularios de acceso de Elementor Pro (versión Premium)
- Includes support for bbPress login forms (Premium version)
- Includes support for Easy Digital Downloads login forms (Premium version)
- Includes support for RegistrationMagic login forms (Premium version)
- Includes support for login forms from the Gravity Forms User Registration add-on (Premium version)
- Includes support for login forms (shortcode forms only) from Paid Memberships Pro (Premium version)
- Incluye compatibilidad para todos y cada uno de los formularios de acceso de terceros (versión Premium) sin necesidad de codificación adicional al agregar tu código TFA al final de tu contraseña
- No menciona ni solicita el segundo factor hasta que el usuario haya sido identificado como uno con el TFA activado (es decir, no se muestra nada a los usuarios que no lo tienen activado)
- Compatible con WP Multisitio (el plugin debe estar activado en la red)
- Interfaz de usuario simplificada y base de código para facilidad de uso y rendimiento.
- Se añadieron una serie de controles de seguridad adicionales al código original
- Alert users if someone appears to have found out their password, as indicated by successfully entering a password but repeatedly entering an incorrect TFA code.
- Códigos de emergencia para cuando pierdas tu teléfono/tableta (versión Premium)
- Cuando utilizas el shortcode de portada (versión Premium), solicita al usuario que introduzca el código TFA actual correctamente para poder activar TFA
- Funciona junto con «WP Members» (formulario de código abreviado)
- Los administradores pueden acceder a los códigos de otros usuarios y activarlos/desactivarlos cuando sea necesario (versión Premium)
¿Por qué usar TFA / 2FA?
¡Lee esto! https://www.wired.com/2012/08/apple-amazon-mat-honan-hacking/
¿Cómo funciona TFA/2FA?
Este plugin utiliza el algoritmo estándar de la industria TFA/2FA TOTP o HOTP para crear contraseñas de un solo uso. Estos son utilizados por Google Authenticator, Authy y muchas otras aplicaciones OTP que puedes implementar en tu teléfono, etc.
Un código TOTP es válido durante un tiempo determinado. Cualquier programa que utilice (es decir, Google Authenticator, etc.) mostrará un código diferente de vez en cuando.
Notas del plugin
Este plugin comenzó a funcionar a principios del 2015 como una bifurcación amigable y una mejora del plugin de «identificación de dos factores» de Oscar Hane.
Capturas
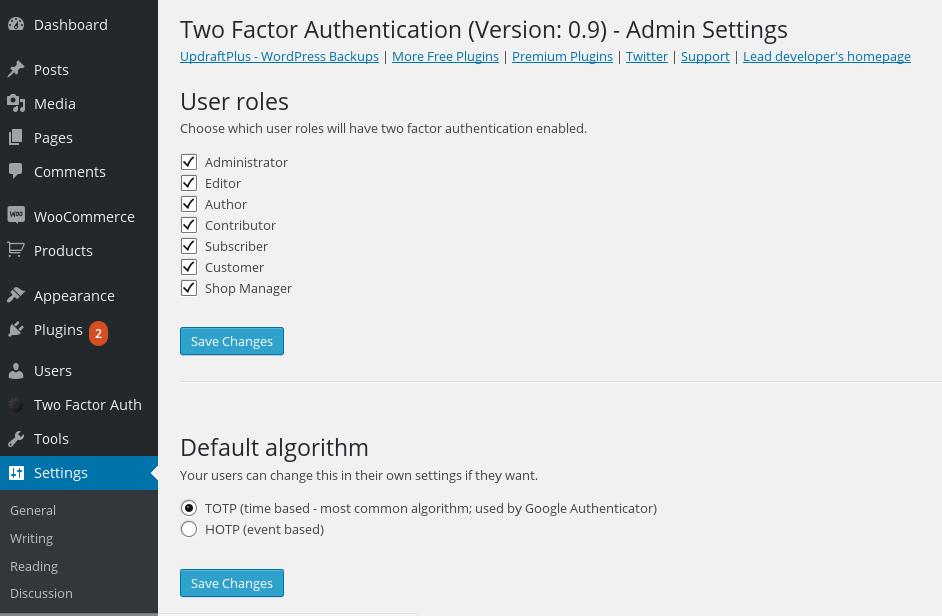
Ajustes de todo el sitio

Ajustes de usuario (escritorio)

Ajustes de usuario (portada, a través de shortcode)
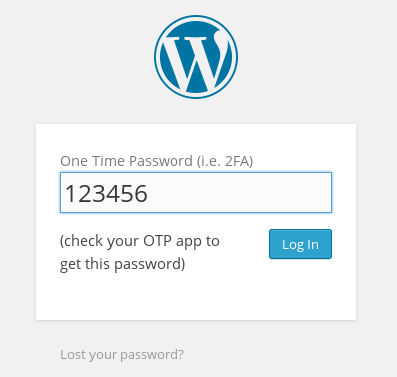
formulario de acceso de WP normal que solicita el código OTP (después de introducir correctamente el nombre de usuario/contraseña)
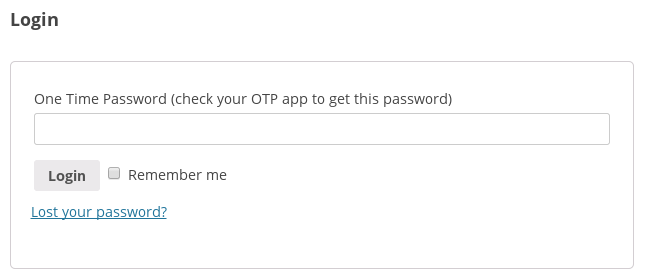
formulario de acceso de WooCommerce que solicita el código OTP (después de introducir correctamente el nombre de usuario/contraseña)

Lo que ve el usuario si abre un código OTP incorrecto en el formulario de acceso normal de WP

Lo que ve el usuario si abre un código OTP incorrecto en el formulario de acceso de WooCommerce
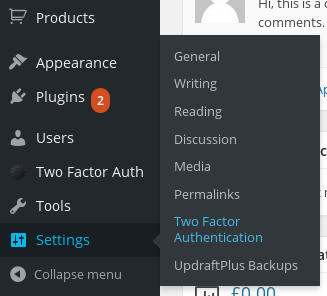
Dónde encontrar los ajustes de todo el sitio en el menú del escritorio
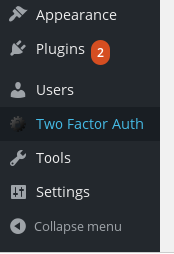
Dónde encontrar los ajustes personales del usuario en el menú del escritorio
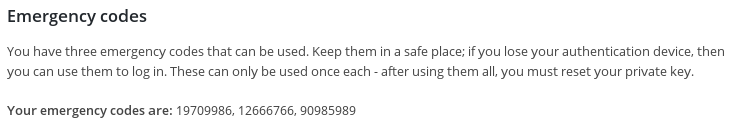
Códigos de emergencia (versión Premium)
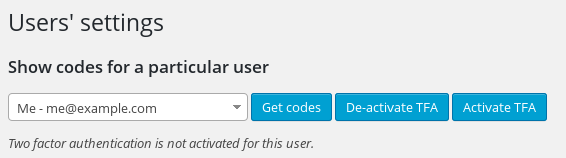
Ajustar los ajustes de otros usuarios como administrador (versión Premium)

Crea tu propio diseño para la página con shortcodes personalizados (versión Premium)
Bloques
Este plugin proporciona 1 bloque.
- Twofactor User Settings
Instalación
Este plugin requiere la versión 5.3 de PHP o superior y es compatible con php-openssl o PHP mcrypt. La gran mayoría de las configuraciones de PHP tendrán uno de estos. Si no es así, pregunta a tu empresa de alojamiento.
- Busca «Identificación de dos factores» en el menú «Plugins» en WordPress.
- Haz clic en el botón «Instalar». (Asegúrate de elegir el correcto)
- Activa el plugin en menú ‘Plugins’ de WordPress
- Busca los ajustes de todo el sitio en Ajustes > Identificación de dos factores; busca tus propios ajustes de usuario en la entrada del menú de nivel superior «Identificación de dos factores».
If you want to add a section to the front-end of your site where users can configure their two-factor authentication settings, use this shortcode: [twofactor_user_settings] . (If you set the attribute show_algorithm_selector to «yes» then it will include an ‘advanced’ settings section allowing the HOTP algorithm to be chosen and not only the default TOTP algorithm, but few people will want this).
FAQ
-
¿Qué es la identificación de dos factores (TFA/2FA)?
-
Básicamente, tiene que ver con proteger tus accesos, de modo que haya más de un eslabón en la cadena que deba romperse antes de que un intruso no deseado pueda ingresar a tu web.
By default, your WordPress accounts are protected by only one thing: your password. If that’s broken, then everything’s wide open.
«Two factor» means adding a second requirement. Usually, this is a code that comes to a device you own (e.g. phone, tablet) – so, someone can’t get into your website without getting hold of your device. You can get a longer answer from Wikipedia.
A veces también se le llama identificación multifactor en lugar de dos factores, porque alguien podría proteger sus sistemas con tantos factores como quisiera.
-
¿Por qué debería importarme?
-
Leer esto: https://www.wired.com/2012/08/apple-amazon-mat-honan-hacking/
-
¿Cómo funciona la identificación de dos factores (TFA/2FA)?
-
Dado que «identificación de dos factores» simplemente significa «un segundo algo es necesario para entrar», esta respuesta depende de la configuración particular. En el caso más común, se muestra un código numérico en tu teléfono, tableta u otro dispositivo. Este código se enviará a través de un SMS; esto depende del funcionamiento de la red de telefonía móvil. Este plugin no utiliza ese método. En su lugar, utiliza un algoritmo matemático estándar para generar códigos que solo son válidos una vez cada uno, o solo durante 30 segundos (según el algoritmo que elijas). Tu teléfono o tableta puede conocer el código después de haberlo configurado una vez (a menudo, simplemente escaneando un código de barras fuera de la pantalla).
-
Qué necesito configurar en mi teléfono/tableta (etc.) para generar los códigos?
-
This depends on your particular make of phone, and your preferences. Google have produced a popular app called «Google Authenticator», which is a preferred option for many people because it is easy to use and can be set up via just scanning a bar code off your screen – follow this link, and ignore the first paragraph that is talking about 2FA on your Google account (rather than being relevant to this plugin).
-
¿Qué pasa si no tengo un teléfono o tableta?
-
Many and various devices and programs can generate the codes. One option is an add-on for your web browser; for example, here are some apps and add-ons for Google Chrome. Wikipedia lists various programs for different computers.
-
Perdí mi dispositivo que tiene códigos de acceso o no funcionan. ¿Qué hacer?
-
Si tu contraseña solía funcionar, pero ya no lo hace, verifica que la hora en tu dispositivo que la genera sea precisa.
Si no puedes acceder y necesitas desactivar la identificación de dos factores, añade esto a tu archivo wp-config.php, usando FTP o el administrador de archivos en tu panel de control de alojamiento:
define('TWO_FACTOR_DISABLE', true);Añadir a continuación de cualquier otra línea que comience con «definir».
Alternativamente, si tienes acceso FTP o cPanel a tu espacio de alojamiento web, puedes desactivar el plugin; consulta este artículo.
-
¿Por qué el plugin no admite el envío del código de dos factores por correo electrónico?
-
Si alguien tiene acceso a su cuenta de correo electrónico, entonces puedes enviar un código de restablecimiento de contraseña mediante los mecanismos de restablecimiento de contraseña integrados en WordPress. Por lo tanto, si el código de dos factores también se envió allí, la capacidad de leer su correo electrónico permite romper ambos factores y, por lo tanto, ya no es realmente una identificación de dos factores.
Algunos usuarios pueden tener identificación de dos factores en su cuenta de correo electrónico, pero esto no se puede conocer ni controlar desde dentro de WordPress, por lo que dar esta opción a los usuarios significa que el administrador no puede ver o hacer cumplir la identificación de dos factores. E incluso en este caso, el correo electrónico a menudo se envía entre servidores sin cifrar, por lo que es susceptible a ataques de intermediario más allá del control de WordPress.
-
¿Qué son HOTP y TOTP?
-
Estos son los nombres de los dos algoritmos matemáticos que se utilizan para crear los códigos especiales. Estos son algoritmos estándar de la industria, ideados por criptógrafos expertos. HOTP es menos popular, pero el dispositivo que genera los códigos no necesita saber la hora correcta (en cambio, los códigos se generan en una secuencia precisa). TOTP es mucho más popular y genera códigos que solo son válidos durante 30 segundos (por lo que su dispositivo necesita saber la hora). Recomendaría TOTP, ya que HOTP puede ser molesto si algo hace que las secuencias no estén sincronizadas.
-
¿Cuál es el shortcode que se debes usar para los ajuste de la portada?
-
[twofactor_user_settings]
-
¡Introduje deliberadamente una contraseña incorrecta y me deja acceder!
-
Tienes una extensión de administrador de contraseñas instalada en tu navegador web, con la contraseña correcta ingresada. Has reemplazado automáticamente tu contraseña incorrecta con la correcta de tu tienda guardada. Este comportamiento ha sido observado y confirmado por varios usuarios. Puedes verificarlo utilizando las herramientas de desarrollo web en tu navegador para ver los datos HTTP enviados a WordPress y observar qué contraseña está realmente en ellos. También puedes abrir un navegador web nuevo sin dicha extensión para volver a probar.
Ten en cuenta que el plugin de identificación de dos factores no tiene ningún mecanismo para comparar o aprobar contraseñas; esto lo hace el núcleo de WordPress. Si se envía la contraseña incorrecta, WordPress se encargará de ello y el acceso no continuará.
Reseñas
Colaboradores y desarrolladores
«Two Factor Authentication» es un software de código abierto. Las siguientes personas han colaborado con este plugin.
Colaboradores«Two Factor Authentication» está traducido en 18 idiomas. Gracias a los traductores por sus contribuciones.
Traduce «Two Factor Authentication» a tu idioma.
¿Interesado en el desarrollo?
Revisa el código , echa un vistazo al repositorio SVN o suscríbete al registro de desarrollo por RSS.
Registro de cambios
1.16.0 – 09/Dec/2025
- FEATURE: Add support for Easy Digital Downloads(EDD) login form
- TWEAK: Resolve a typo in the emergency code usage email notification text
1.15.5 – 28/Jun/2025
- FIX: Function WP_Block_Type_Registry::register was called incorrectly
- FIX: Fix regression in 1.15.1 which could result in displaying settings incorrectly, with checkboxes hidden
- FEATURE: Add support for RegistrationMagic login forms
1.15.2 – 25/Apr/2025
- TWEAK: Fix regression in 1.15.1 in parsing of multisite capabilities
1.15.1 – 12/Apr/2025
- TWEAK: Replace use of maybe_unserialize()
- TWEAK: Add support for shortcode-based login forms from Paid Memberships Pro (Premium version)
1.15.0 – 13/Dec/2024
- TWEAK: The ‘twofactor_user_settings’ shortcode will now not include the «advanced» settings section (with a selector for the TOTP or HOTP algorithm) in the settings output. You can revert to the previous behaviour by adding the attribute show_algorithm_selector=»yes» to the shortcode (e.g. [twofactor_user_settings show_algorithm_selector=»yes»] ).
1.14.27 – 25/Nov/2024
- FIX: 1.14.26 broke saving settings on a front-end page via the shortcode
- TWEAK: Purge empty members of the tfa_incorrect_code_attempts list, to prevent unnecessary growth; and key by user ID, not user login
1.14.26 – 13/Nov/2024
- TWEAK: Resolve a language deprecation notice on WP 6.7 and non-default language
1.14.25 – 11/Nov/2024
- FIX: Fix a regression in 1.14.24 Premium in the handling of empty query strings in redirect URLs when running on PHP <= 7.4 (if on such versions, please see https://www.php.net/eol.php ).
1.14.24 – 24/Oct/2024
- TWEAK: Redirection when TFA is compulsory (Premium feature) should exclude the logout link
- FIX: An issue that prevented turning on TFA when the redirect user URL is set
1.14.23 – 25/Jun/2024
- TWEAK: Do not require TFA codes for API requests authenticated via an application password
- TWEAK: Improve formatting of «trust this device» checkbox
1.14.22 – 28/Nov/2023
- FIX: Fix a fatal error that occurred due to a failure to process a WP_Error object on an Affiliates WP login form
- TWEAK: Further improve styling when used on Ultimate Member login forms
- TWEAK: Force unsetting of disabled property before triggering click event
1.14.21 – 01/Nov/2023
- TWEAK: Improve styling when used on Ultimate Member login forms
1.14.20 – 27/Oct/2023
- FEATURE: Add support (Premium version) for Ultimate Member login forms
1.14.19 – 14/Oct/2023
- TWEAK: Change the «not available for your user» message to be more appropriate when output on pages without login
- TWEAK: Prevent PHP coding notice when logging an incorrect login
- TWEAK: Updated bundled updater library to latest series
1.14.18 – 30/Aug/2023
- TWEAK: The settings for making TFA compulsory (Premium feature) have had their layout and descriptions changed to enhance clarity.
- TWEAK: The filter simba_tfa_apply_redirect_in_admin has had its default value changed from false to true. This means that when users are forcibly redirected to a setup page, this happens in the admin area too.
1.14.17 – 26/Aug/2023
- FEATURE: Notify user if multiple wrong TFA codes used (which indicates someone has their password)
- FEATURE: Add a Gutenberg block for the [twofactor_user_settings] shortcode.
- TWEAK: Resolve PHP 8.2 deprecation notice introduced in 1.14.15
- TWEAK: Do not look for a TFA code when validating an existing cookie
- TWEAK: Tweak HTML structure where private key is printed to reduce likelihood of copy/paste introducing an unwanted space
- TWEAK: Do not consider empty strings when turning on database encryption
- TWEAK: Update updater library to current version (resolves some PHP 8.2 deprecation notices)
1.14.16 – 08/May/2023
- FIX: Fix an error on PHP 7.2 introduced in 1.14.15 (PHP 7.2 was end-of-lifed by the PHP group in 2020, so please update! https://www.php.net/eol.php ).
- TRANSLATIONS: Update French and Italian translations (thank you to the translators)
- TWEAK: Correct string identifier for «TFA is configured to not be available for this role» text
- TWEAK: Make role names translatable in one place where they were not
1.14.15 – 05/May/2023
- FEATURE: Encrypt TFA secret keys that are stored in the database (extra protection in case of your database being hacked)
- FIX: Fix handling of login forms on a page where Gravity Forms was loaded in the JavaScript environment but was not providing the login form
- TWEAK: Make use of hash_equals function when comparing TOTP codes to prevent timing comparisons
1.14.14 – 24/Mar/2023
- FIX: When on a multisite on a non-main site, the link shown to the network administration for the plugin was wrong
- TWEAK: Cache whether a user is using TFA when moving from the username field, in order to reduce delay when presenting TFA field
- TWEAK: Userlist related css file version to be based on its file’s time.
- TWEAK: Add config utility methods and tweak registering settings.
- TWEAK: Add a span with CSS class simba_tfa_otp_login_help to the «check your OTP app to get this password» text
- TWEAK: Add support for CozmosLabs Profile Builder login forms
- TWEAK: Fix some minor problems related to translation domain handling and untranslatable phrases
- TWEAK: Suppress message that these are your personal settings for less-privileged users
- TWEAK: Ensure that user roles are translated
- TWEAK: Updated French translation, thanks to @madmax4ever
1.14.13 – 15/Nov/2022
- TWEAK: Improve styling of trusted device control when used with Gravity Forms User Registration Login forms
1.14.12 – 12/Nov/2022
- FEATURE: Add support (Premium version) for Gravity Forms User Registration Login forms
- TWEAK: Fix PHP notice with the AffiliateWP plugin if a user has not enabled TFA
1.14.11 – 25/Oct/2022
- TWEAK: Provide a link to the user’s TFA settings on the user profile page
- TWEAK: Fix a typo (being/begin)
- TWEAK: In the admin settings, show more clearly in the «Make two factor authentication compulsory» section the dependence upon the earlier «Make two factor authentication» section
1.14.10 – 10/Oct/2022
- TWEAK: Only load Simba_TFA_Login_Form_Integrations class if not already present
- TWEAK: Hide all HTML entities that have
hide-when-displaying-tfa-inputclass when 2FA code prompt at login time.
1.14.9 – 07/Oct/2022
- FEATURE: Allow the site owner to choose when policy enforcement (Premium) begins for already-existing users
1.14.8 – 05/Oct/2022
- TWEAK: Move JavaScript for displaying QR codes and handling trusted devices into its own file, for better CSP compatibility
1.14.7 – 28/Sep/2022
- TWEAK: Dynamic (non-explicitly declared) properties are deprecated as of PHP 8.2
- TWEAK: Update bundled Select2 4.0 version to current release
- TWEAK: Move JavaScript for administering other users into its own file, for better CSP compatibility
- TWEAK: When a device is already trusted, show this information as plain text, not in the TFA field
- TWEAK: When the TFA input field is shown, hide error messages from previous logins
- TWEAK: If the AJAX call to check on OTP status fails, show a user-visible message
- TWEAK: Add .localdomain hostnames to those permitted to have trusted devices
- TWEAK: Relabel «Get codes» button
- TWEAK: Add some filters allowing easier customisation of messages displayed
- TWEAK: Show only the base32 encoding of the private key (unless the shortcode explicitly specified otherwise), since for a long time now this is what all known apps accept
1.14.6 – 02/Sep/2022
- TWEAK: The TFA login script is loaded on the login script if a user has enabled the Two Factor Authentication feature.
1.14.5 – 01/Sep/2022
- TWEAK: Gave Premium mentions their own CSS class
1.14.4 – 15/Aug/2022
- FIX: Multisite Plugin Settings link to work in particular site plugins page for main site admin
- REFACTOR: Make the Simba Two Factor Authentication library more re-usable
- REFACTOR: Place premium auto-update code in the main file
- TWEAK: Introduce simba_tfa_get_option_site_id and simba_tfa_skip_adding_options_menu_entry filters
1.14.3 – 26/Jan/2022
- TWEAK: Change internal translation building and loading mechanism
- TWEAK: «https://» is not a translatable string
- TWEAK: Load translations even if aborting due to incompatible PHP version
- TWEAK: Update updater libraries to current versions
1.14.1 – 08/Nov/2021
- REFACTOR: The constants SIMBA_TFA_PLUGIN_DIR and SIMBA_TFA_PLUGIN_URL have been abolished. If you had hand-coded any code that used them, then you will want to review and test your customisations carefully first. This applies for all refactoring items and internal changes mentioned below.
- REFACTOR: Internal plugin directory structure changed
- TWEAK: Fix a potential PHP coding notice in 1.13.0 when an administrator viewed a user’s QR code
1.13.0 – 01/Nov/2021
- REFACTOR: Complete re-organisation of all Premium code. If you had hand-coded any code which interacted with it, you will want to review and test your customisations carefully first. This applies for all refactoring items and internal changes mentioned below.
- REFACTOR: Abolished the class Simba_TFA_Plugin_Admin_Dashboard_Integration
- REFACTOR: Moved some TOTP/HOTP-specific methods out of Simba_Two_Factor_Authentication into Simba_TFA_Provider_TOTP
- TWEAK: Class TFA_Frontend renamed to Simba_TFA_Frontend
- TWEAK: The constant SIMBA_TFA_PLUGIN_FILE is no longer used internally and has been abolished
- TWEAK: Move Premium plugin update loader into the main Premium class
- TWEAK: Factor out all Premium features into individual classes
- TWEAK: The method tfa_is_available_and_active() has been removed.
- TWEAK: The method Simba_TFA_Provider_TOTP::getPanicCodesString() has been renamed to Simba_TFA_Provider_TOTP::get_emergency_codes_as_string()
1.12.3 – 22/Oct/2021
- FIX: Fix the twofactor_user_qrcode shortcode in the Premium version
1.12.2 – 21/Oct/2021
- FIX: Prevent load-order related fatal error (regression since 1.12.0) on sites that did not have AUTH_KEY defined in wp-config.php
- TWEAK: Update updater library in Premium version to latest version
- TWEAK: Introduce templating method for better code organisation
1.12.1 – 18/Oct/2021
- REFACTOR: Continuing the major re-factor of the plugin’s internal classes. If you had hand-written custom PHP code that hooks into any internal classes, you will want to review your customisations carefully first.
- TWEAK: Update .pot file
1.12.0 – 16/Oct/2021
- REFACTOR: Major re-factor of the plugin’s internal classes. If you had hand-written custom PHP code that hooks into any internal classes, you will want to review your customisations carefully first.
- TWEAK: Harmonise wording on trusted devices label
- TWEAK: Remove redundant hex2bin compatibility for no-longer-supported PHP versions
1.11.0 – 14/Sep/2021
- FEATURE: (Premium) Add new anti-bot feature for WooCommerce login forms: do not include the login form within the page HTML (making them invisible to most bots), bringing it back via JavaScript. The feature needs to be activated within the plugin settings.
1.10.4 – 27/Jul/2021
- TWEAK: Fix a couple of minor visual regressions in the WooCommerce login form TFA field layout
1.10.3 – 28/Jun/2021
- FIX: Incorrect object reference in Affiliate WP integration (regression in 1.10.0)
1.10.2 – 26/Jun/2021
- TWEAK: The script tfa_frontend.php now uses an external JavaScript file (better compatibility with with content security policies)
1.10.1 – 25/Jun/2021
- FIX: Fix a bug in the Premium Elementor integration introduced in 1.10.0.
1.10.0 – 15/Jun/2021
- REFACTOR: Integrate the previously-separate WooCommerce/Affiliates-WP handlers in the main handler, eliminating redundant/duplicate code. Eliminate the internal concept of different form types by re-coding the few «type one»s as type twos. Separate login-form specific data from code.
1.9.6 – 04/Jun/2021
- FEATURE: Support bbPress login forms (Premium version)
1.9.5 – 26/May/2021
- TRANSLATIONS: Update bundled Spanish translation (es_ES) in Premium release
1.9.4 – 25/May/2021
- FIX: Prevent an issue identifying the username field when on a page with both Affiliates WP login and registration forms, when the login form displayed second
1.9.3 – 14/Apr/2021
- FIX: In the Premium version, when appending the TFA code to the password on third-party login forms with no direct support, only usernames were accepted for the login (not email addresses)
1.9.2 – 20/Mar/2021
- TWEAK: When checking if a user has TFA enabled on a login page, perform the same sanitisation on the username as WP core, so that if the user mistypes their username (which WP accepts) e.g. by prefixing a space, then they will still be asked for their TFA code (instead of jumping straight to an error for not supplying one)
- TRANSLATIONS: Added an Italian translation, thanks to Edoardo Di Leginio
1.9.1 – 15/Feb/2021
- TWEAK: Correct the «for» attribute of the «mark as trusted» text label on the WooCommerce login form
1.9.0 – 09/Feb/2021
- FEATURE: (Premium) If TFA is required for a user, and they have not yet set it up, then force them to be redirected to a configured URL
- TWEAK: Replace the deprecated jQuery.click() and .change() methods
1.8.8 – 16/Jan/2021
- TWEAK: Replace the deprecated jQuery.unbind() and .focus() methods
- TWEAK: If the free version is active, then throw an error if trying to activate the Premium version, explaining what needs to be done
1.8.7 – 11/Jan/2021
- TWEAK: Update jQuery document ready, click and submit styles to one not deprecated in jQuery 3.0, and replace :first pseudo-selector with .first()
- TWEAK: Now marked as supporting PHP 5.6+ (now that PHP 8.0 is out)
- TWEAK: Update to the latest version of the bundled updater library (paid versions), which adds integration with WP 5.5+’s auto-updater
1.8.6 – 15/Sep/2020
- FEATURE: Add a ‘TFA’ column also to the Users screen in the WP network admin dashboard (multisite installs)
- TWEAK: Update the bundled updater library (paid versions) to the current release
1.8.5 – 29/Aug/2020
- TWEAK: Fix the «for» attribute of the «trusted» text label on the WooCommerce login form
- TWEAK: If a website’s wp-login.php is available under multiple hosts without CORS enabled between them, then AJAX calls would fail; this is now resolved by using a relative URL instead
- TWEAK: Update bundled updater libraries on Premium version (improving compatibility with WP 5.5+’s update settings)
1.8.4 – 26/May/2020
- TWEAK: Updare .pot file; now both the first two parameters to _n() are also included in the aggregation process
1.8.2 – 23/May/2020
- FIX: If the site owner was requiring a correct code to be supplied for activation, then this was also being required for de-activation
- TWEAK: Introduce simbatfa_enforce_require_after_check filter, allowing developers to selectively disable the «require TFA after X days» check
- TWEAK: Update .pot file
1.8.0 – 18/Apr/2020
- FEATURE: Add support in the paid version for Elementor login forms
- TWEAK: Updater in paid version now will make checks on availability without needing login
- TWEAK: Update updater class to current release
1.7.4 – 19/Mar/2020
- TWEAK: Adjust how the trusted field is referenced from JavaScript, fixing IE11 compatibility
- TWEAK: Introduce the filter simba_tfa_required_for_user
1.7.3 – 03/Mar/2020
- TWEAK: Provide non-plural alternative for trusted device phrase
- TWEAK: Mark as supporting WP 5.4
1.7.2 – 13/Feb/2020
- TWEAK: Update message about what to do with translations
1.7.1 – 14/Jan/2020
- FIX: Missing file in 1.7.0 (free) release
1.7.0 – 14/Jan/2020
- FEATURE: (Premium version): Add an optional TFA section to the WooCommerce account details section in «My Account»
- TWEAK: Fix div tag balancing issue in settings output
- TWEAK: Update WooCommerce integration to adjust to DOM changes in WooCommerce 3.8
- TWEAK: Update .pot file
1.6.4 – 12/Nov/2019
- TWEAK: On wp-login.php on WordPress 5.3, the password field was not hiding when the TFA field opened
- TWEAK: Update .pot file
- TWEAK: Add data-lpignore attribute to TFA field to indicate to LastPass that it is not a password field
1.6.3 – 18/Oct/2019
- FIX: The ‘trusted users’ option display in the settings defaulted to showing as enabled, whereas in fact the default setting is disabled
- TWEAK: Mark as compatible with WP 5.3
1.6.2 – 11/Sep/2019
- FIX: On multisites, administration of site users who were not present on the main site was not possible
- TWEAK: Introduce the WP action simba_tfa_activation_status_saved to allow developers to respond to activation status changes
- TWEAK: Update updater class to 1.8 series
1.6.1 – 10/Aug/2019
- TWEAK: Response to an attempt to turn TFA on can now include an «error» attribute if the attempt failed due to failure to supply the current code
1.6.0 – 08/Aug/2019
- FEATURE: (Premium version) By using the parameter style=»require_current» with the shortcode twofactor_user_settings_enabled, the user will only be able to activate TFA if they enter the current TFA code
- TWEAK: Remove the incorrect suffix «(Premium)» (double-suffix in the actual Premium version) that appeared in the plugin title in 1.5.6
1.5.6 – 06/Aug/2019
- TWEAK: Allow customisation of a particular message via a filter simbatfa_message_you_should_verify
- TWEAK: Replace «eachother» with «each other»
1.5.5 – 30/Jul/2019
- TWEAK: Force a global context when creating the initial Simba_Two_Factor_Authentication object, to work around direct accesses from components that do not set the scope correctly
1.5.4 – 17/Jul/2019
- FEATURE: (Premium version) – allow the site administrator to forbid users who have compulsory TFA to turn it off (supplementing the additional capability to prevent them logging in)
1.5.3 – 22/Jun/2019
- TWEAK: When using your final emergency code (Premium version), and viewing your settings (which regenerated new ones), then if you did not follow the advice to reset your private key, you would get the same codes as before. This might be thought undesirable (though is not a security flaw, as the emergency codes are no more guessable the second time around than the first). This behaviour has now been changed.
1.5.2 – 08/Jun/2019
- TWEAK: When php-mcrypt was not installed, pressing the «Reset private key» link in a user’s settings would cause an unnecessary PHP notice, and display a wrong «current code» for a few seconds.
1.5.1 – 05/May/2019
- FEATURE: Support any login form (Premium version) via appending the TFA code onto the end of the password. This allows support even of login forms coded in a way that make integrations (that aren’t hacks or inordinate amounts of work-around code) impossible (e.g. PeepSo)
- TWEAK: Minor wording tweak in the explanation of how TOTP works.
1.4.12 – 18/Apr/2019
- TWEAK: Add a filter simba_tfa_localisation_strings allowing further customisation of front-end strings
- TWEAK: Add an extra instructional message in the «Make two factor authentication compulsory» section (Premium) to explain how to cope with existing users
- TWEAK: Cope with the user entering spaces in their two-factor code (TOTP protocol codes are numbers only, but some apps apparently display formatting and users are not aware)
- TWEAK: Mark as supporting WP 5.2
1.4.11 – 08/Mar/2019
- FIX: On multisites, the user search should search on all sites, not just the main one
1.4.10 – 01/Mar/2019
- TWEAK: Introduce a filter, simba_tfa_management_capability, allowing the WP capability (default: manage_options) required by a user to manage the plugin to be changed. (Be careful – giving the ability to manage could potentially mean the ability to lock any user out).
1.4.9 – 20/Feb/2019
- SECURITY: The security fix in version 1.4.7 was faulty and failed to completely fix the problem; it is now resolved in this release. Our apologies for the double update.
1.4.8 – 16/Feb/2019
- FIX: On some multisite setups, the link to the site-wide administration settings went to the wrong place
1.4.7 – 06/Feb/2019
- SECURITY: If a user’s WordPress account username was in the form of an email address, and if their actual account email address was something different, and TFA was set up on that account, and used the «username» (that looked like an email address) to login, then TFA controls upon login on that account would be ineffective. Other accounts were not affected (regardless of whether you login by email or not). This vulnerability was inherited from the original «Two Factor Auth» plugin that this plugin was forked from, and so is present in all versions before this one.
1.4.6 – 05/Feb/2019
- FIX: When displaying a user’s trusted devices in the admin page, the time that a device was trusted until was not shown correctly (instead, it showed the current time)
- FIX: Removing the first trusted device in a list did not always work
- TWEAK: Display «(none)» when there are no trusted devices
1.4.4 – 04/Feb/2019
- FEATURE: Trusted devices are now listed in the user’s admin page, allowing them to see and remove trust from their devices.
- TWEAK: Updated .pot file
1.4.3 – 28/Jan/2019
- FIX: The «Trusted devices» functionality (Premium) checkbox was not appearing when activated
- TWEAK: Add a missing translation domain to a phrase
1.4.1 – 25/Jan/2019
- FEATURE: Trusted devices: A site owner can now choose to allow particular user levels (e.g. admins, editors) to mark devices as ‘trusted’ and thereby exempt from needing to enter a TFA code for a chosen number of days. This feature is off by default and requires https (i.e. SSL) on the login form and cookies to be kept in the trusted device.
- FIX: Fix a regression in 1.4.0 whereby when a site owner viewed another user’s current code, it could later self-update with the wrong user’s value
- TWEAK: Add the robustness in parsing broken JSON present on the standard WP login form to other login forms
- TWEAK: Various internal code documentation improvements
- TWEAK: Suppress mcrypt deprecation notices in places where we would use an alternative if it was not present
- TWEAK: Bumped the support requirement up to WP 3.4. I’m not aware of anything done to break it on 3.3, but this is the official requirement (it’s very hard to test old WP versions as they don’t run on modern webserver stacks)
1.4.0 – 24/Jan/2019
- FEATURE: Where the current OTP code is displayed (during setup), this will now self-update automatically (i.e. without needing a manual press on the «update» link).
- TWEAK: Various improvements to the layout and text of the setup page to help make the process more understandable
- TWEAK: The current code is shown next to the UI option for enabling TFA
- TWEAK: Prevent a PHP notice if AUTH_KEY was not defined (on some very old WP installs)
1.3.13 – 18/Dec/2018
- SECURITY: Fix a logged-in CSRF vulnerability reported by Martijn Korse (www.bitnesswise.com). Due to a missing nonce check, if an attacker was able to persuade a personally-targeted victim who was currently logged in to their WordPress account to visit a personally-crafted (for the individual victim) page in the same browser session, then the attacker would be able to de-activate two-factor authentication for the victim on that WordPress site (thus leaving the targeted account protected by the user’s password, but not by a second factor – the absence of a request for a TFA code would be apparent on the user’s next login). This vulnerability was inherited from the original «Two Factor Auth» plugin that this plugin was forked from, and so is present in all versions before this one.
- TWEAK: Some minor code-tidying
- TWEAK: Update bundled Premium updater library to current version (1.5.10)
1.3.12 – 14/Dec/2018
- TWEAK: Prevent a PHP debugging notice when $pagenow is not set
1.3.11 – 04/Dec/2018
- FEATURE: Add a ‘TFA’ column on the Users screen in the WP admin dashboard to display TFA status, thanks to Enrico Sorcinelli.
1.3.10 – 30/Nov/2018
- FIX: TFA codes were not being requested on the login form on a WooCommerce dedicated order payment page (i.e. /checkout/order-pay/123456/?pay_for_order=true&key=wc_order_blahblahblah) (meaning that if a user had TFA activated, login would fail).
- TWEAK: Prevent a PHP notice if AUTH_SALT was not defined (on some very old WP installs)
1.3.9 – 30/Oct/2018
- SECURITY: If you were not using the recommended option of requiring 2FA for XMLRPC requests, then an attacker could potentially also bypass requirements for 2FA on ordinary logins (i.e. only need the password). Such users will want to immediately update, though we recommend that all users do. This vulnerability was inherited from the original «Two Factor Auth» plugin that this plugin was forked from, and so is present in all versions before this one.
1.3.8 – 25/Oct/2018
- TWEAK: Update the updater class in the Premium version to the current release (1.5.6)
1.3.7 – 15/Oct/2018
- TWEAK: Try to mitigate plugins on the login page which cause JavaScript exceptions by enqueuing our scripts earlier.
1.3.6 – 04/Oct/2018
- TWEAK: Add attribute autocomplete=»off» on the WooCommerce login form TFA field (was already present for regular WP login form)
- TRANSLATION: Added Portuguese (Brazilian) translation, courtesy of Dino Marchiori
1.3.5 – 02/Oct/2018
- TWEAK: Some code-styling consistency clean-ups
- TWEAK: Allow one more window’s tolerance by default for codes from devices running fast
1.3.4 – 11/Sep/2018
- FIX: Sometimes a TML widget login form could fail to work because of a changed/unexpected DOM tree
- FIX: Some further breakage in TML had occurred, causing login buttons to require to be pressed twice
1.3.3 – 31/Jul/2018
- FIX: Restore support for «Theme My Login», which had been broken by unannounced changes in TML 7.x
- TRANSLATIONS: Update .pot file
1.3.2 – 31/May/2018
- TWEAK: Add the simbatfa_check_tfa_requirements_ajax_response and simbatfa_verify_code_and_user_result filters to allow over-riding of the response to the «TFA required?» question and the TFA check itself by developers
1.3.1 – 25/May/2018
- FIX: The WooCommerce 3.3+ login form was requiring two clicks on the ‘Log In’ button
- TWEAK: The progress spinner had disappeared on WooCommerce 3.3+
1.3.0 – 05/Apr/2018
- FEATURE: (Premium version) Integration with the WP-Members login form, https://wordpress.org/plugins/wp-members/ . N.B. WP-Members does not pass on the real error message upon a login failure, but displays its own hard-coded message that the username/password were wrong; so you’ll see this even if it was really the TFA code that was wrong.
- TWEAK: Change the permission check for editing other users (Premium version) to edit_users (instead of the previous update_plugins, intended just as a proxy for «is an admin»)
- TWEAK: Stop using the deprecated jQuery.parseJSON method
- TWEAK: Change a string that was not in a translatable form
- TWEAK: Update the updater class in the Premium version to the current release (1.5.1)
1.2.35 – 28/Nov/2017
- TWEAK: Upon front-end settings save, do jQuery(document).trigger(‘tfa_settings_saved’), allowing the user to respond to the action (e.g. reload page)
- TWEAK: Suppress mcrypt deprecation notices on PHP 7.1 (we already know it is deprecated, and already use openssl if it is not installed)
1.2.34 – 08/Nov/2017
- TWEAK: Remove calls to the deprecated screen_icon() function
- TWEAK: Remove some unnecessary bundled translation files
- TWEAK: Add some translation files not previously included in the Premium version
- TWEAK: Update bundled Premium updater library to current (1.5.0)
1.2.33 – 09/Oct/2017
- FIX: The available/required settings for super-admins on multisite installs were not saving (Premium feature)
- FIX: When the admin fetched another user’s current QR code, it embedded the wrong username (which was a cosmetic issue only – the code itself was correct) (Premium feature)
1.2.32 – 06/Oct/2017
- TWEAK: Update bundled updater in Premium to latest version (1.4.8)
1.2.31 – 05/Oct/2017
- FEATURE: (Relevant to Premium version): Automatically generate new emergency codes when they run out, including upon view of settings if there are none (e.g. on upgrade from free to Premium)
- TWEAK: Code-styling consistency tweaks
1.2.30 – 18/Sep/2017
- FIX: TML shortcode forms were not working properly for non-TFA users
1.2.29 – 16/Sep/2017
- FIX: Prevent double-show of TFA field on TML default login page (regression)
- FIX: Restore functionality on TML shortcode forms (regression, likely due to changes in TML)
- TWEAK: Restore the spinner to proper size on all forms
- TWEAK: A few very minor code style clean-ups
1.2.27 – 29/Aug/2017
- TWEAK: Add the new ‘PHP Requires’ header to readme.txt
- TWEAK: Correct a couple of wrong translation domain references
1.2.26 – 08/Aug/2017
- FIX: Do not request TFA code on TML reset password form (regression, likely due to changes in TML)
- APOLOGIES: 1.2.25 was a faulty release that would block logins. You should immediately update.
1.2.24 – 05/Aug/2017
- TWEAK: Update to the latest version of the updater library (Premium)
1.2.23 – 15/Jun/2017
- TWEAK: Allow admins to reset users’ private keys (Premium)
1.2.22 – 23/May/2017
- TWEAK: Update updater library to current version (Premium)
- TWEAK: Use higher-quality spinner image
- COMPATIBILITY: Mark as compatible with WP 4.8
1.2.21 – 22/Feb/2017
- TWEAK: Update jquery-qrcode library to latest release (0.14.0)
- TWEAK: Explicitly encode spaces in WordPress usernames (apparently resolves a problem with a particular iPhone app)
1.2.20 – 17/Feb/2017
- TWEAK: Work around a bug seen with strlen() on one particular PHP install
- FIX: The line purporting to show the current UTC time was in fact taking your WordPress timezone into account. It has now been adjusted to show both to avoid ambiguity.
- FIX: 1.2.18 used a PHP 5.4+ only function, whereas we support PHP 5.3+
1.2.17 – 09/Feb/2017
- FIX: Fix support for login widgets from Theme My Login
1.2.16 – 30/Jan/2016
- FIX: Fix issue whereby if you were already logged in and managed to visit a login form, you would not be asked for a TFA code
1.2.15 – 23/Jan/2017
- FEATURE: Add support for login widgets from Theme My Login
- UPDATER: (Premium version): update to the latest updater class, including the new ability to automatically update
= 1.2.14 …
